中秋節快樂啊!但還是得繼續碰密碼學w
今天要來解三題,繼續了解AES各個步驟是怎麼進行的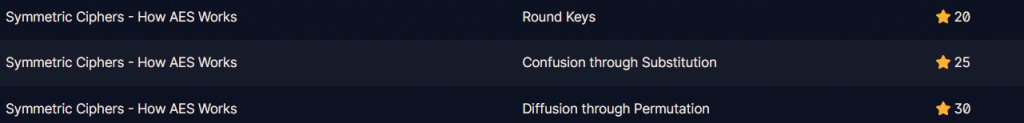
網址 : https://cryptohack.org/courses/symmetric/aes3/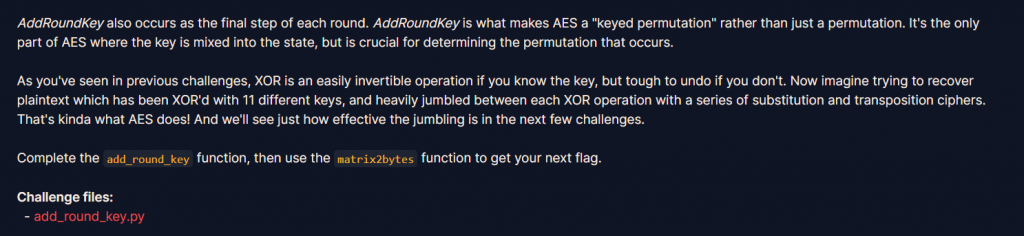
題目在介紹Round Keys的過程
it XORs the current state with the current round key
之後題目給了state跟round_key,要我們完成xor的過程,輸出xor後的結果作為flag
利用迴圈一個一個做xor加到encrypt字串,最後回傳字串
state = [
[206, 243, 61, 34],
[171, 11, 93, 31],
[16, 200, 91, 108],
[150, 3, 194, 51],
]
round_key = [
[173, 129, 68, 82],
[223, 100, 38, 109],
[32, 189, 53, 8],
[253, 48, 187, 78],
]
def add_round_key(s, k):
encrypt = ""
for i in range(0, 4) :
for j in range(0, 4):
encrypt += chr(s[i][j]^k[i][j])
return encrypt
print(add_round_key(state, round_key))
encrypt = ""
for i in range(0, 4) :
for j in range(0, 4):
encrypt += chr(s[i][j]^k[i][j])
可寫成
encrypt = ''.join([chr(s[i][j] ^ k[i][j]) for i in range(4) for j in range(4)])
flag : crypto{r0undk3y}
網址 : https://cryptohack.org/courses/symmetric/aes4/
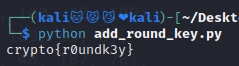
這題在講Substitution的過程
最後題目給了sbox跟inverse_sbox還有state
要我們把state跟inverse_xbox做替代的動作得出flag
也就是flag += inverse_sbox[state[i][j]]
inv_s_box = (
0x52, 0x09, 0x6A, 0xD5, 0x30, 0x36, 0xA5, 0x38, 0xBF, 0x40, 0xA3, 0x9E, 0x81, 0xF3, 0xD7, 0xFB,
0x7C, 0xE3, 0x39, 0x82, 0x9B, 0x2F, 0xFF, 0x87, 0x34, 0x8E, 0x43, 0x44, 0xC4, 0xDE, 0xE9, 0xCB,
0x54, 0x7B, 0x94, 0x32, 0xA6, 0xC2, 0x23, 0x3D, 0xEE, 0x4C, 0x95, 0x0B, 0x42, 0xFA, 0xC3, 0x4E,
0x08, 0x2E, 0xA1, 0x66, 0x28, 0xD9, 0x24, 0xB2, 0x76, 0x5B, 0xA2, 0x49, 0x6D, 0x8B, 0xD1, 0x25,
0x72, 0xF8, 0xF6, 0x64, 0x86, 0x68, 0x98, 0x16, 0xD4, 0xA4, 0x5C, 0xCC, 0x5D, 0x65, 0xB6, 0x92,
0x6C, 0x70, 0x48, 0x50, 0xFD, 0xED, 0xB9, 0xDA, 0x5E, 0x15, 0x46, 0x57, 0xA7, 0x8D, 0x9D, 0x84,
0x90, 0xD8, 0xAB, 0x00, 0x8C, 0xBC, 0xD3, 0x0A, 0xF7, 0xE4, 0x58, 0x05, 0xB8, 0xB3, 0x45, 0x06,
0xD0, 0x2C, 0x1E, 0x8F, 0xCA, 0x3F, 0x0F, 0x02, 0xC1, 0xAF, 0xBD, 0x03, 0x01, 0x13, 0x8A, 0x6B,
0x3A, 0x91, 0x11, 0x41, 0x4F, 0x67, 0xDC, 0xEA, 0x97, 0xF2, 0xCF, 0xCE, 0xF0, 0xB4, 0xE6, 0x73,
0x96, 0xAC, 0x74, 0x22, 0xE7, 0xAD, 0x35, 0x85, 0xE2, 0xF9, 0x37, 0xE8, 0x1C, 0x75, 0xDF, 0x6E,
0x47, 0xF1, 0x1A, 0x71, 0x1D, 0x29, 0xC5, 0x89, 0x6F, 0xB7, 0x62, 0x0E, 0xAA, 0x18, 0xBE, 0x1B,
0xFC, 0x56, 0x3E, 0x4B, 0xC6, 0xD2, 0x79, 0x20, 0x9A, 0xDB, 0xC0, 0xFE, 0x78, 0xCD, 0x5A, 0xF4,
0x1F, 0xDD, 0xA8, 0x33, 0x88, 0x07, 0xC7, 0x31, 0xB1, 0x12, 0x10, 0x59, 0x27, 0x80, 0xEC, 0x5F,
0x60, 0x51, 0x7F, 0xA9, 0x19, 0xB5, 0x4A, 0x0D, 0x2D, 0xE5, 0x7A, 0x9F, 0x93, 0xC9, 0x9C, 0xEF,
0xA0, 0xE0, 0x3B, 0x4D, 0xAE, 0x2A, 0xF5, 0xB0, 0xC8, 0xEB, 0xBB, 0x3C, 0x83, 0x53, 0x99, 0x61,
0x17, 0x2B, 0x04, 0x7E, 0xBA, 0x77, 0xD6, 0x26, 0xE1, 0x69, 0x14, 0x63, 0x55, 0x21, 0x0C, 0x7D,
)
state = [
[251, 64, 182, 81],
[146, 168, 33, 80],
[199, 159, 195, 24],
[64, 80, 182, 255],
]
def sub_bytes(state, inv_s_box):
flag = ""
new_state = [[chr(inv_s_box[i])for i in row] for row in state ]
for i in range(4):
for j in range(4):
flag += new_state[i][j]
return flag
print(sub_bytes(state, inv_s_box))
flag : crypto{l1n34rly}
網址 : https://cryptohack.org/courses/symmetric/aes5/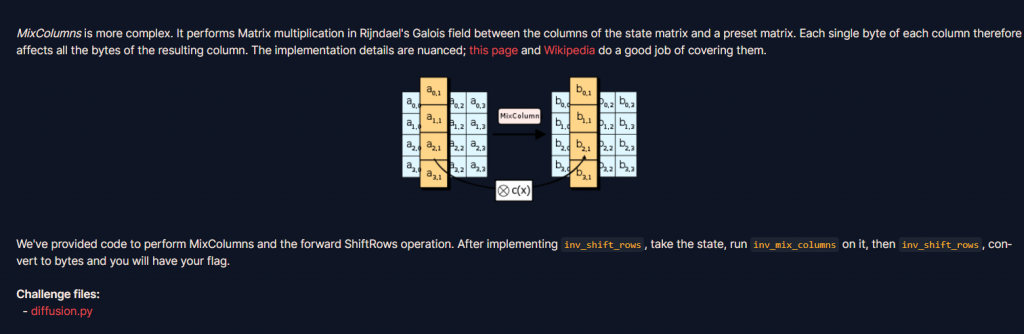
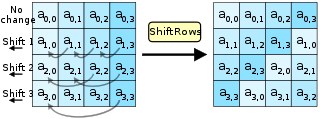
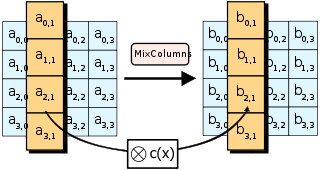
這題在講ShiftRows 跟 MixColumns 的過程
最後題目給了一個已經做了ShiftRows跟MixColumns後的state,目標為還原它得到flag
shift_rows過程為
第一行向左位移0
第二行向左位移1
第三行向左位移2
第四行向左位移3
所以我們就還原
第二行向右位移1
第三行向右位移2
第四行向右位移3
其實就是把shift_row中兩邊相反就ok惹
s[0][1], s[1][1], s[2][1], s[3][1] = s[1][1], s[2][1], s[3][1], s[0][1]
變成
s[1][1], s[2][1], s[3][1], s[0][1] = s[0][1], s[1][1], s[2][1], s[3][1]
def inv_shift_rows(s):
s[1][1], s[2][1], s[3][1], s[0][1] = s[0][1], s[1][1], s[2][1], s[3][1]
s[2][2], s[3][2], s[0][2], s[1][2] = s[0][2], s[1][2], s[2][2], s[3][2]
s[3][3], s[0][3], s[1][3], s[2][3] = s[0][3], s[1][3], s[2][3], s[3][3]
# learned from http://cs.ucsb.edu/~koc/cs178/projects/JT/aes.c
xtime = lambda a: (((a << 1) ^ 0x1B) & 0xFF) if (a & 0x80) else (a << 1)
def mix_single_column(a):
# see Sec 4.1.2 in The Design of Rijndael
t = a[0] ^ a[1] ^ a[2] ^ a[3]
u = a[0]
a[0] ^= t ^ xtime(a[0] ^ a[1])
a[1] ^= t ^ xtime(a[1] ^ a[2])
a[2] ^= t ^ xtime(a[2] ^ a[3])
a[3] ^= t ^ xtime(a[3] ^ u)
def mix_columns(s):
for i in range(4):
mix_single_column(s[i])
def inv_mix_columns(s):
# see Sec 4.1.3 in The Design of Rijndael
for i in range(4):
u = xtime(xtime(s[i][0] ^ s[i][2]))
v = xtime(xtime(s[i][1] ^ s[i][3]))
s[i][0] ^= u
s[i][1] ^= v
s[i][2] ^= u
s[i][3] ^= v
mix_columns(s)
state = [
[108, 106, 71, 86],
[96, 62, 38, 72],
[42, 184, 92, 209],
[94, 79, 8, 54],
]
def main():
inv_mix_columns(state)
inv_shift_rows(state)
for i in range(4):
for j in range(4):
print(chr(state[i][j]),end="")
if __name__ == "__main__":
main()
flag : crypto{d1ffUs3R}
AES過程為: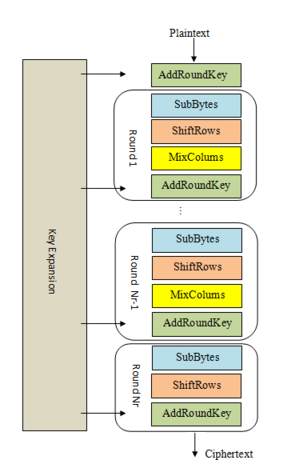
AddRoundKey
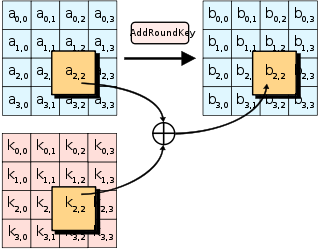
b[2][2] = a[2][2] ^ k[2][2]
subBytes
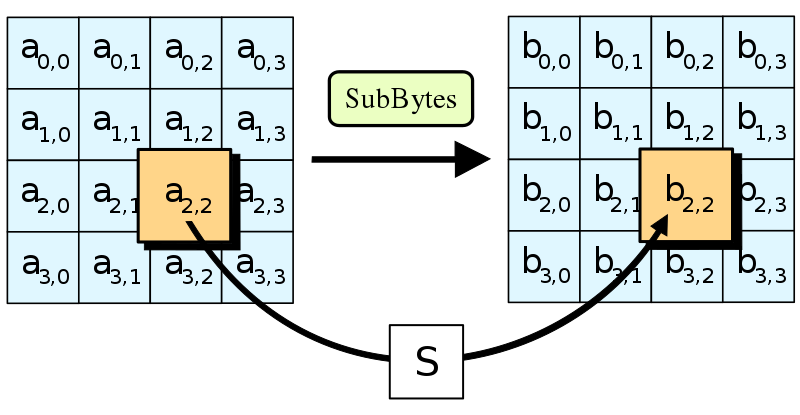
new_state = s_box[state[2][2]]
shiftRows
Mixcolumns
詳細的可以參考"AES進階加密"這篇文章
今天透過題目詳細了解了昨天AES過程中提到的名詞
AES進階加密 : https://ithelp.ithome.com.tw/articles/10289999?sc=iThelpR
Crypto : https://hackmd.io/@kevinjone25/HknsSVi5_#%E4%B8%80%E4%BA%9Bpy%E5%87%BD%E5%BC%8F
